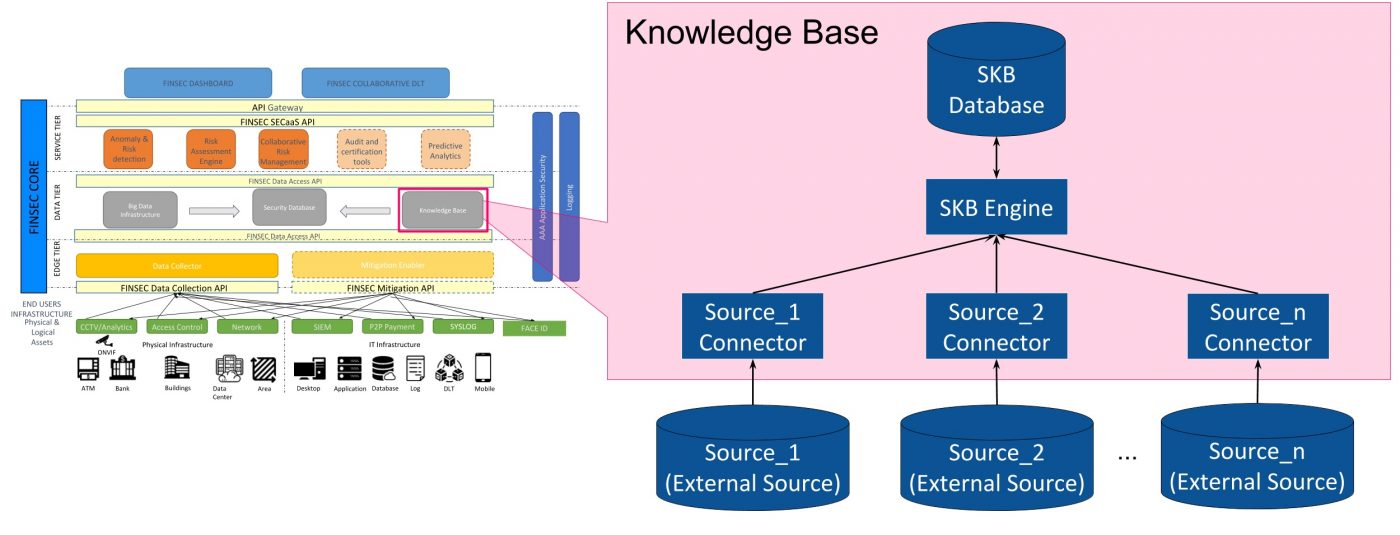
The architecture of the cybersecurity knowledge base. DDoS: distributed... | Download Scientific Diagram

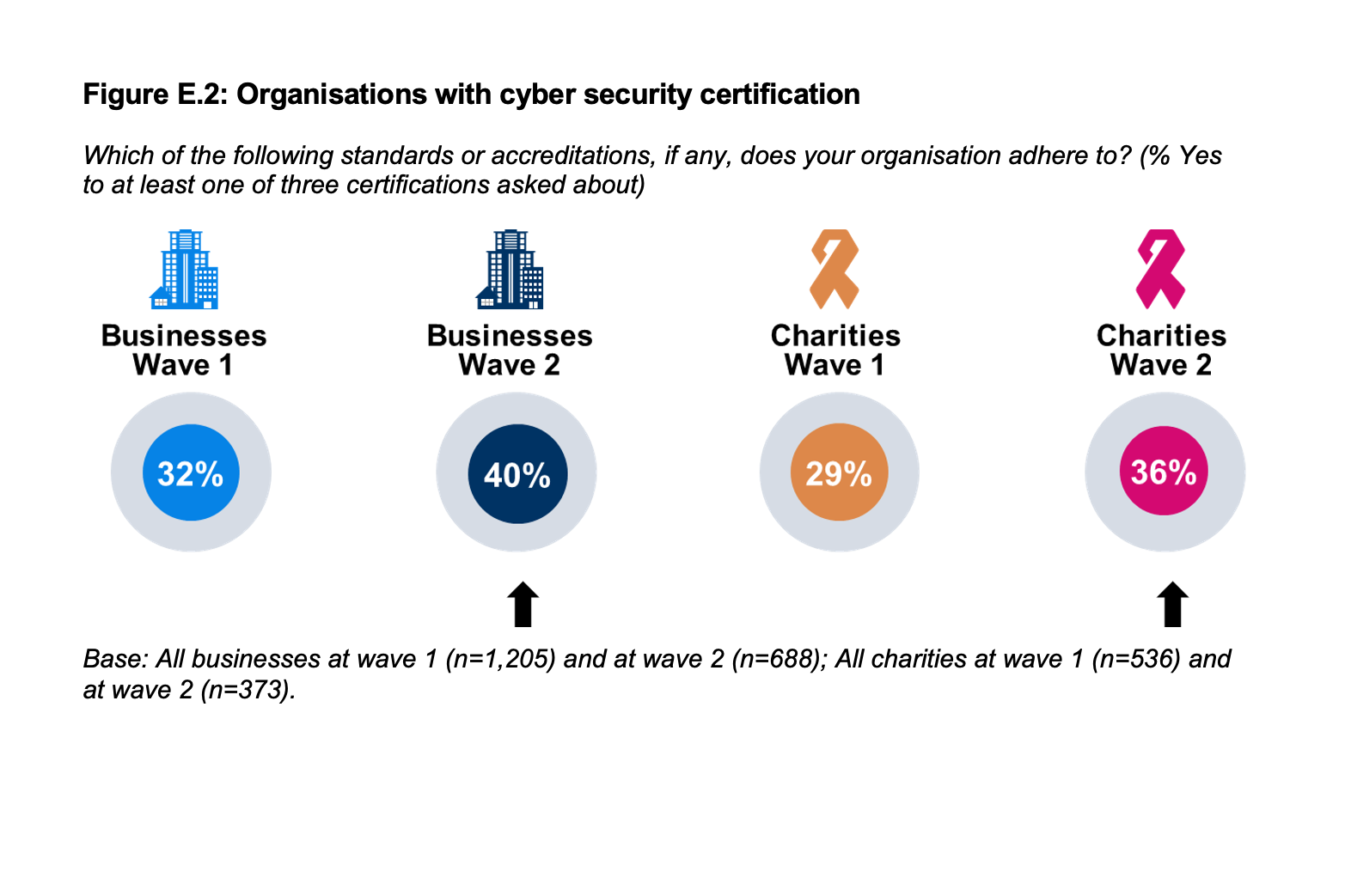
Companies need to invest more in cybersecurity, 5G to propel internet user base to 25 bn in 2023: Rajesh Pant, Government News, ET Government
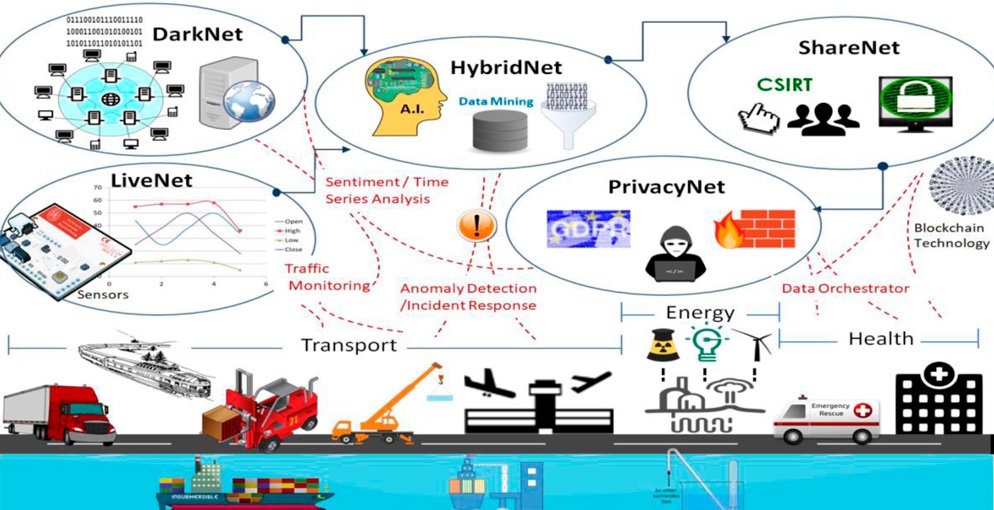
CYBERSANE - CYBER SECURITY INCIDENT HANDLING, WARNING AND RESPONSE SYSTEM FOR THE EUROPEAN CRITICAL INFRASTRUCTURES - Fundación Valenciaport